Platform
Use Cases
Many Possibilities. One Platform.
AI and Automation
The Always-on Incrementality Platform
Solutions
Teams
Built for your whole team.
Industries
Trusted by all verticals.
Mediums
Measure any type of ad spend
Use Cases
Many Possibilities. One Platform.
AI and Automation
The Always-on Incrementality Platform
Teams
Built for your whole team.
Industries
Trusted by all verticals.
Mediums
Measure any type of ad spend
The Chronology of Evil

The mobile advertising industry is one of the fastest growing industries in history. It is also the first truly global industry, where a marketer from Finland may have over one hundred million customers in the US by working with a media vendor based in China (for example). This industry has grown from $0 to over $200 billion dollars in just over 10 years becoming a very lucrative industry to defraud.
Mobile advertising has become infested with fraudulent players, ranging from small affiliates, to larger companies who develop technologies to steal advertising budgets by gaining credit for results. Incrementality analysis finds no value in fraud.

During the early days of mobile advertising, Apps had no method to track installs and the most common method of media buying was based on clicks (CPC Pricing).
As the ad took a substantial portion of the screen, it became common for fraudulent publishers to force users to click ads by triggering a click for each screen touch.
Fat Fingers completely vanished with the rise of install tracking using mobile attribution companies, allowing advertisers to track and pay for installs (CPI pricing)
With the availability of install tracking “Cost Per Install” (CPI) became the de facto default pricing model for app promotion.
Fraudulent publishers and ad networks used or mixed incentivized inventories, incentivizing users to download apps by offering a reward.
As Advertisers measured the “success” of a campaign by the number of installs - blending incentivized inventories that produces almost no LTV allowed publishers to show good performance to unsuspecting advertisers.
With Advertisers happy to pay per installs, some marketers ignored obvious signs of fraud. For example - seeing 100,000,000 clicks per day in a country with a smaller population.
As Attribution providers gave credit to whoever generated the last click - fraudulent publishers started triggering clicks in the background of the device, sometimes triggering multiple click urls for several app campaigns, so that if and once the user does install any of the apps who’s clicks have been triggered - the attribution provider will give the credit to the fraudulent publisher.
With more and more Advertisers and attribution companies being aware of click spamming, fraudulent publishers started getting questions about the flat distribution and the sheer volume of clicks.
The Android operating system offered an opportunity for fraudsters with a feature called “Broadcast”, broadcasting the start of an install of a new app.
Sophisticated fraudsters used code to inject an affiliate click URL once they knew an app was starting to be installed, thus being the last “click” before the app was opened.
Cheetah Mobile, one of the largest mobile publishers was caught red handed conducting click injection.
The graph below shows examples of click-to-install-time (in seconds) normal distribution, click spam distribution, and click injection.
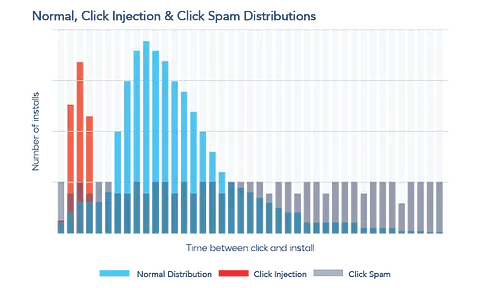
Click Spamming and Click Injection is relatively simple to catch with an excel and some heuristics. Clicks and Install farms can be harder, as those may be operated by people - showing up as real installs, who’s whole intention to interact with ads or install the apps is to earn money from the Advertiser.
YouTube has numerous guides about “how to start your own app farm” and you can even find ready to go phone farms on eBay.
Most of these fraudsters have a small impact on overall spend, hence, it’s become easy for these fraudsters to slip below the radar.
3rd party anti-fraud solutions help identify these by tracing traffic coming from a single location / IP - however, the smart “farmers” know this and work to renew their IPs regularly to not get blocked.
Why bother with a phone farm, when you can develop a bot that simulates a real user ?
Bot inventory accounts for a large portion of internet inventories. Some bots are good (i.e. google crawlers) , but some are malicious and meant to find potential breaches.
Solutions such as WhiteOps (currently humansecurity.com), TrafficGuard, interceptd are examples of dedicated anti-fraud solutions, protecting Advertisers by sampling traffic patterns, or by connecting to other analytics/attribution solutions to provide detection and prevention in real time.
The most sophisticated and hardest to catch. Spoofing has been a term used for conversions that show a complete user funnel, including in-app events, purchases, all coming with real device parameters such as device ID and so on. The trouble is - none of it happened. Fraudsters can spoof a click, an install event, and in-app activity, by reverse engineering how a real conversion flow works, and by constructing the same path in real devices without the user needing to do anything, but by distributing their code into unsuspecting devices.
Wandera recently found that Mintegral, one of the most popular SDKs, has been engaged in spoofing at a large scale.
Attribution solutions such as Adjust, Appsflyer, Kochava, Branch, and Singular, have also been offering some anti-fraud solutions - some, as part of their core offering, and some as a premium feature offered to Advertisers.
INCRMNTAL is not an anti fraud platform. Our incrementality measurement platform helps marketers measure value. Our platform provides recommendations and actionable insights where the most value can be found.
If you want to learn more, visit INCRMNTAL or book a demo today!
The Chronology of Evil
The mobile advertising industry is one of the fastest growing industries in history. It is also the first truly global industry, where a marketer from Finland may have over one hundred million customers in the US by working with a media vendor based in China (for example). This industry has grown from $0 to over $200 billion dollars in just over 10 years becoming a very lucrative industry to defraud.
Mobile advertising has become infested with fraudulent players, ranging from small affiliates, to larger companies who develop technologies to steal advertising budgets by gaining credit for results. Incrementality analysis finds no value in fraud.

Maor is the CEO & Co-Founder at INCRMNTAL. With over 20 years of experience in the adtech and marketing technology space, Maor is well known as a thought leader in the areas of marketing measurement. Previously acting as Managing Director International at inneractive (acquired by Fyber), and as CEO at Applift (acquired by MGI/Verve Group)